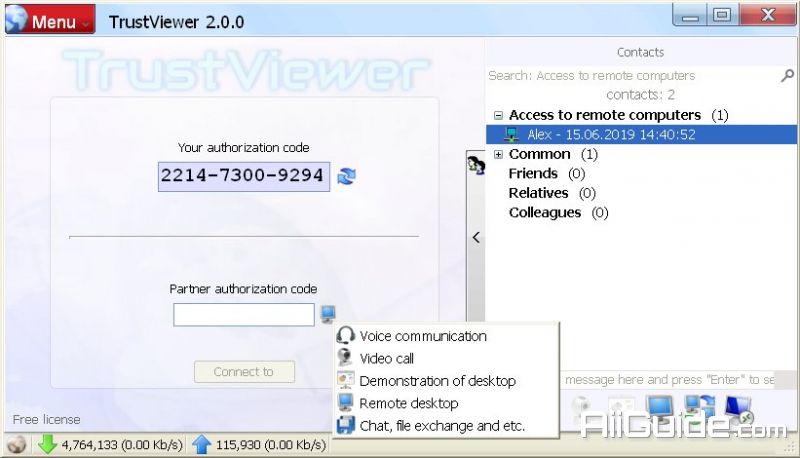
Download TrustViewer 2 for Windows - Allows you to connect and access remote computers to perform system maintenance tasks or assist in troubleshooting
TrustViewer is a software that allows you to connect and access remote computers to perform system maintenance tasks or assist in troubleshooting technical problems on computers. TrustViewer is often used to manage remote applications as well as help customers solve service or product issues.
The idea behind TrustViewer was to provide direct point-to-point connectivity; Therefore, TrustViewer is familiar software of IT professionals or computer technical support staff. In addition, TrustViewer does not require configuration or pre-installed features, as long as your computer has a stable Internet connection.
In addition to the remote computer connection software, the emulator applications are also interested in many people, such as Windroy used to play games or run Android applications on the computer, the advantage of Windroy is its ability Support on many operating systems, support full screen mode, support Flash, high resolution and many computer devices accompanying.
TrustViewer allows you to share and transfer files with other users. This feature should be useful for the technical support team working in shifts as well as when your customers encounter errors that cannot reproduce data. TrustViewer does not require you to provide personal data: the software provides an authentication code that takes effect in 5 minutes and expires as soon as you finish the session.
Features of TrustViewer
The opportunity to set their own organizations on their servers free dedicated proxy server, thus allowing the program through the firewall and NAT proxy, as well as to control incoming and outgoing traffic associated with the use of the program TrustViewer.
Using the program is really safe: the complete work does not require authorization or enter of other personal data, and when connecting on our servers is not saved IP-address or another information identifying your computer; when connecting to a remote computer a random temporary identifier is used
The participant's computer is connected directly (the web server is only used for orchestration), forming a secure tunnel based on the SSL / TLS protocols and their similar protocols.
System Requirements
- Supported OS: Windows 7/8/10
- Free Hard Disk Space: 150 MB or more